Pentesting Report Template
Pentesting Report Template - These vulnerabilities may exist in operating systems,. In most cases, both humans and automated. Penetration testing, also known as pen testing or ethical hacking, is a systematic process of testing computer systems, networks, and applications to find security weaknesses. Choose v3 (new version) for the latest. Evaluate the security of your infrastructure with reliable testing methods. Watch this webinar to learn how to get the most out of your penetration test and what to expect from a penetration test. Introduction to penetration testing definition and purpose penetration testing, or pen testing, is the process of simulating cyberattacks on a system, network, or application to. In this guide, we'll explore the fundamentals of penetration testing, its importance in cybersecurity, and how it fits into the software development lifecycle (sdlc). Penetration testing (pen testing) is a simulated cyberattack designed to identify security vulnerabilities and test an organization’s defenses. A penetration test, also known as a pen test, is a simulated cyber attack against your computer system to check for exploitable vulnerabilities. There are different types of penetration testing, depending upon the goal of the organization which include: Penetration testing, also known as pen testing or ethical hacking, is a systematic process of testing computer systems, networks, and applications to find security weaknesses. Penetration testing, or pen testing, is an attempt to evaluate the security of an it infrastructure by safely trying to exploit vulnerabilities. Understanding penetration testing in cyber security at its core, penetration testing (a.k.a., pentesting) is a simulation. Choose v3 (new version) for the latest. Network (external and internal), wireless, web application, social engineering,. Black box, grey box, and white box. They can examine whether a system is robust enough to withstand attacks from authenticated and. Penetration testing or pen testing is a type of security testing used to cover vulnerabilities, threats and risks that an attacker could exploit in software applications,. Watch this webinar to learn how to get the most out of your penetration test and what to expect from a penetration test. Discover the types of penetration tests: They can examine whether a system is robust enough to withstand attacks from authenticated and. There are different types of penetration testing, depending upon the goal of the organization which include: Penetration tests usually simulate a variety of attacks that could threaten a business. Penetration testing is a form of ethical hacking. Network (external and internal), wireless, web application, social engineering,. In this guide, we'll explore the fundamentals of penetration testing, its importance in cybersecurity, and how it fits into the software development lifecycle (sdlc). Pentesting (penetration testing) is a simulated cyber attack conducted to identify security vulnerabilities in a system, network, or application and assess its resilience against. Introduction to penetration. Watch this webinar to learn how to get the most out of your penetration test and what to expect from a penetration test. Discover our certifications pentest+ pentest+ comptia pentest+ is the most comprehensive certification covering all penetration testing stages. Penetration testing is a form of ethical hacking. The purpose of this simulated attack is. Enhance your security posture with. Penetration testing, or pen testing, is an attempt to evaluate the security of an it infrastructure by safely trying to exploit vulnerabilities. It’s designed to replicate the creativity and persistence of real. They can examine whether a system is robust enough to withstand attacks from authenticated and. Penetration tests usually simulate a variety of attacks that could threaten a business.. There are different types of penetration testing, depending upon the goal of the organization which include: Penetration tests usually simulate a variety of attacks that could threaten a business. Reporting helps you patch them before true hackers. Introduction to penetration testing definition and purpose penetration testing, or pen testing, is the process of simulating cyberattacks on a system, network, or. Understanding penetration testing in cyber security at its core, penetration testing (a.k.a., pentesting) is a simulation. Choose v3 (new version) for the latest. In this guide, we'll explore the fundamentals of penetration testing, its importance in cybersecurity, and how it fits into the software development lifecycle (sdlc). Penetration testing (pen testing) is a simulated cyberattack designed to identify security vulnerabilities. Penetration testing, aka pen testing or ethical hacking, attempts to breach a system's security for the purpose of vulnerability identification. Penetration testing is a form of ethical hacking. In this guide, we'll explore the fundamentals of penetration testing, its importance in cybersecurity, and how it fits into the software development lifecycle (sdlc). Penetration testing, often called “pentesting,” is an essential. Introduction to penetration testing definition and purpose penetration testing, or pen testing, is the process of simulating cyberattacks on a system, network, or application to. Penetration tests usually simulate a variety of attacks that could threaten a business. Pentesting (penetration testing) is a simulated cyber attack conducted to identify security vulnerabilities in a system, network, or application and assess its. Discover our certifications pentest+ pentest+ comptia pentest+ is the most comprehensive certification covering all penetration testing stages. There are different types of penetration testing, depending upon the goal of the organization which include: Penetration testing (pen testing) is a simulated cyberattack designed to identify security vulnerabilities and test an organization’s defenses. Introduction to penetration testing definition and purpose penetration testing,. Enhance your security posture with cobalt's fast and scalable penetration testing services, backed by a team of 450+ experts to identify and remediate vulnerabilities effectively. Evaluate the security of your infrastructure with reliable testing methods. Penetration testing, aka pen testing or ethical hacking, attempts to breach a system's security for the purpose of vulnerability identification. Choose v3 (new version) for. Black box, grey box, and white box. When the process is complete, you'll identify weak spots in your plans. Network (external and internal), wireless, web application, social engineering,. Penetration tests usually simulate a variety of attacks that could threaten a business. It’s designed to replicate the creativity and persistence of real. Watch this webinar to learn how to get the most out of your penetration test and what to expect from a penetration test. In this guide, we'll explore the fundamentals of penetration testing, its importance in cybersecurity, and how it fits into the software development lifecycle (sdlc). Understanding penetration testing in cyber security at its core, penetration testing (a.k.a., pentesting) is a simulation. Enhance your security posture with cobalt's fast and scalable penetration testing services, backed by a team of 450+ experts to identify and remediate vulnerabilities effectively. You’ll learn about the different types of penetration tests, why it’s critical, how the process works, and what exactly an attacker is thinking or trying to achieve during an engagement. Evaluate the security of your infrastructure with reliable testing methods. In the context of web application. Penetration testers are security professionals skilled in the art of ethical hacking, which is the use of hacking tools and techniques to fix security weaknesses rather than cause. It involves a methodical process where cybersecurity. Penetration testing is a form of ethical hacking. Reporting helps you patch them before true hackers.Pentest Report Template Word
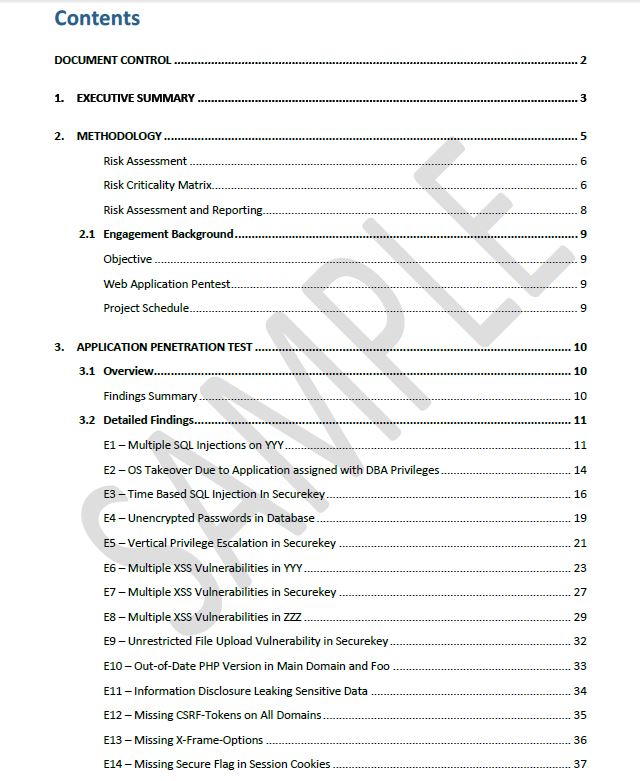
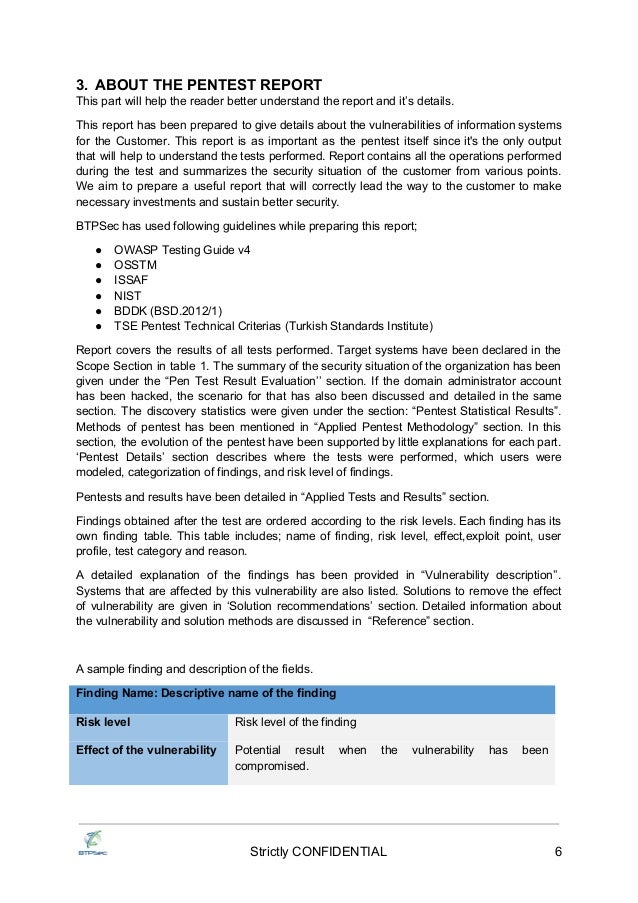
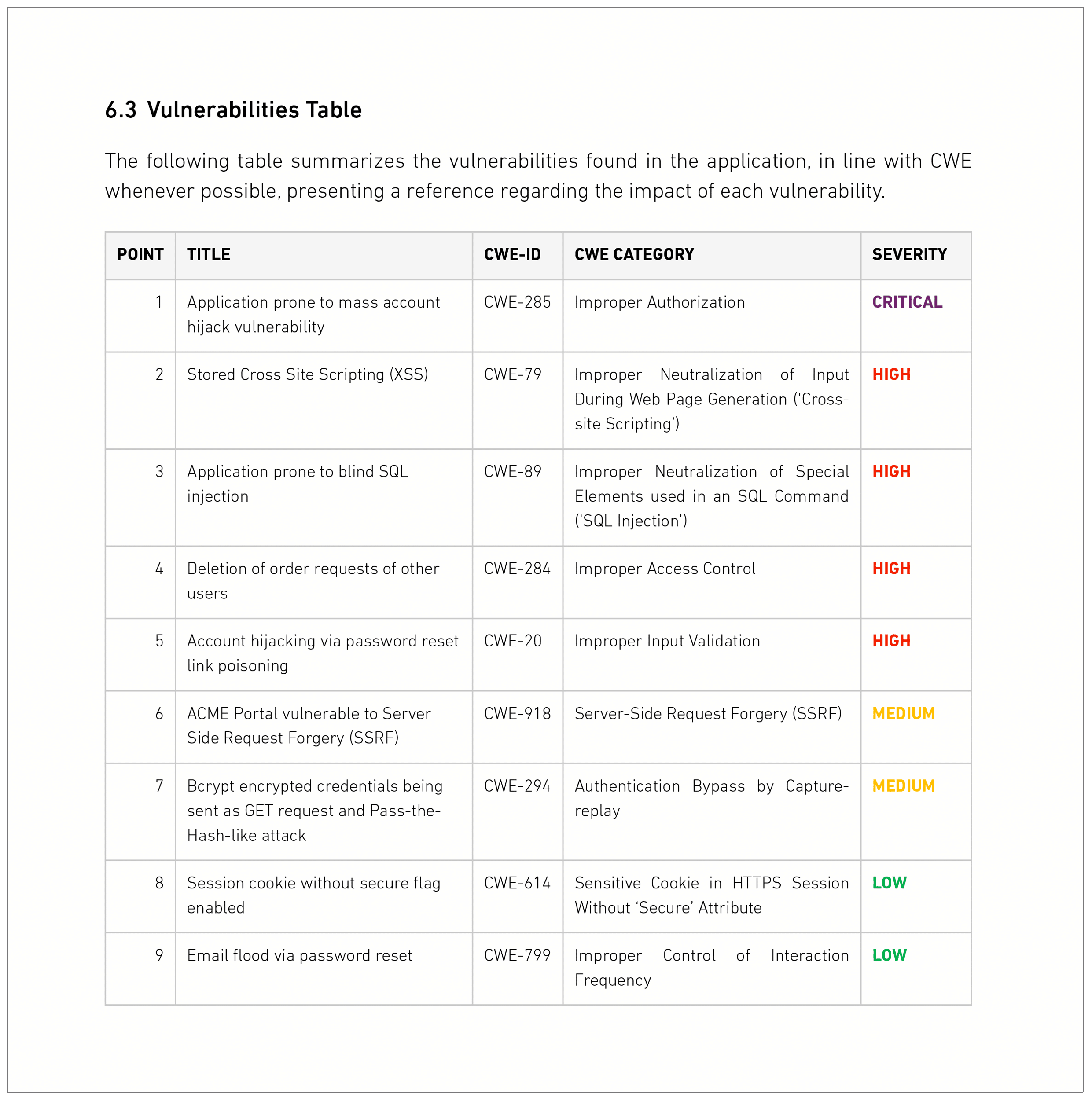
Pentesting Report PDF Vulnerability Test
Pentesting Report Template
How to Write a Pentesting Report With Checklist
Editable Test Report Template
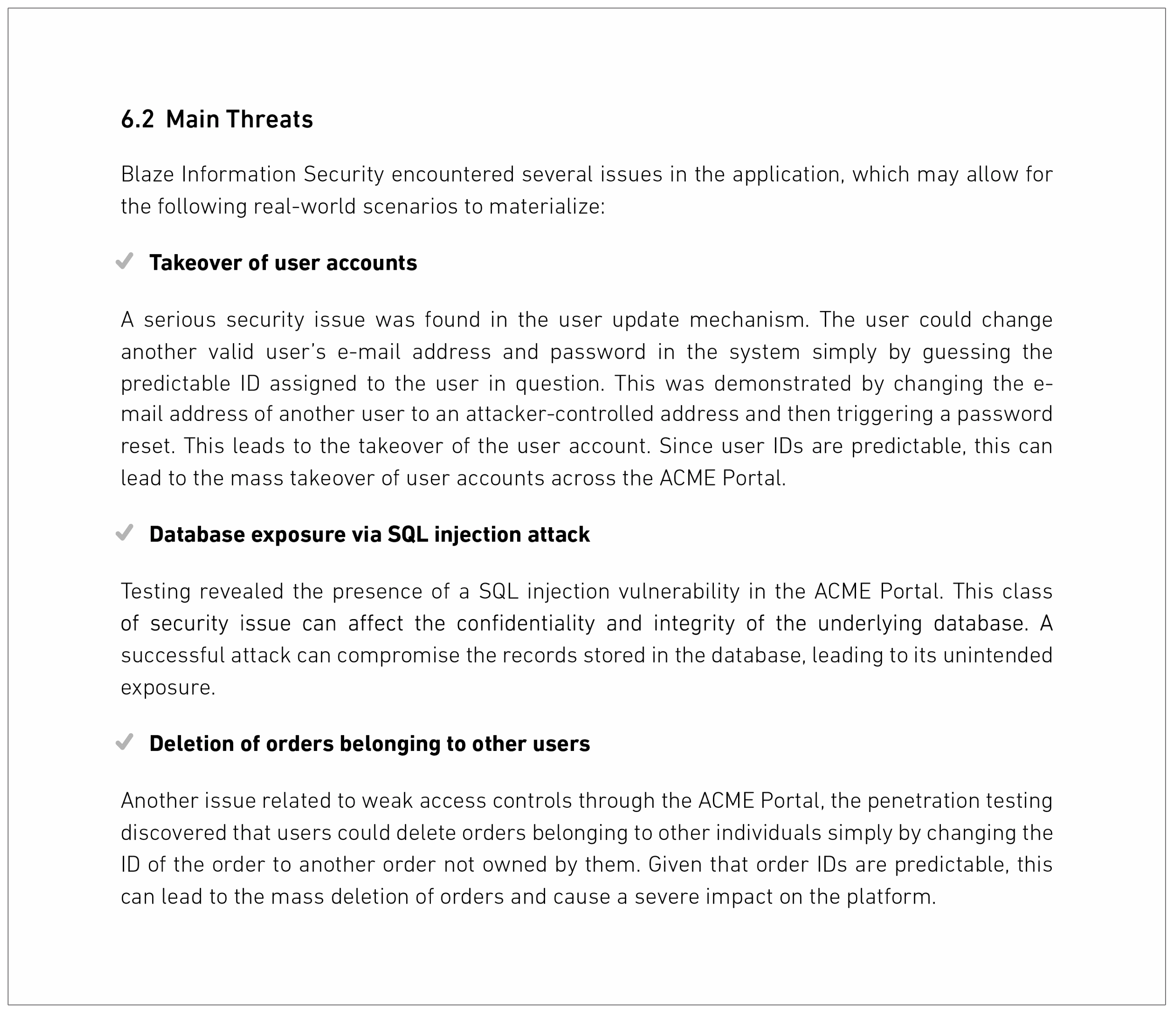
What Does A Testing Report Look Like?
What To Expect From A Testing Report?
Sample Pentesting Report
Pentesting Report PDF Test Data Transmission
Test Report Template prntbl.concejomunicipaldechinu.gov.co
A Penetration Test, Also Known As A Pen Test, Is A Simulated Cyber Attack Against Your Computer System To Check For Exploitable Vulnerabilities.
Discover Our Certifications Pentest+ Pentest+ Comptia Pentest+ Is The Most Comprehensive Certification Covering All Penetration Testing Stages.
These Vulnerabilities May Exist In Operating Systems,.
Penetration Testing, Aka Pen Testing Or Ethical Hacking, Attempts To Breach A System's Security For The Purpose Of Vulnerability Identification.
Related Post: